How Telemedicine Apps Work: Architecture, Data Flow, and System Design Explained
A telemedicine app is not a video call with a medical logo. It is a distributed system that moves protected health information between four environments in under 200 milliseconds while staying inside HIPAA boundaries. Here is exactly how it works, layer by layer, with the tech stack, the data flow, and the numbers that matter.

Manish Patel
As Head of Tech and Client Success at Acquaint Softtech, a software development partner with 1,300+ projects delivered across 13 years, I have spent the last decade reviewing the architecture diagrams of telemedicine platforms built by other teams and rebuilding the ones that broke. Most of them broke for the same reason: the founding team treated how a telemedicine app works as a product question when it is an engineering question. Video calling is the easy part.
The hard part is moving Protected Health Information (PHI) between patients, clinicians, Electronic Health Record (EHR) systems, and insurance payers without breaking latency, consent, or compliance. I have seen three seed-stage health startups burn 18 months rebuilding because they got the data flow wrong on day one. This article explains how telehealth software product development actually works end to end, the tech stack that survives 2026 scale, and the decision points that separate a platform that scales to 10,000 daily consultations from one that crashes at 300.
- Founders and CTOs planning a scalable telemedicine platform.
- Hospital and healthcare teams evaluating custom vs ready-made telehealth solutions.
- Engineering teams entering healthcare and learning telemedicine system requirements.
- Clinical operations leaders wanting clarity on telehealth platform architecture and features.
The Problem → Agitation → SolutionProblem: Founders, Chief Technology Officers (CTOs), and product leads think a telemedicine app is a video Software Development Kit (SDK) wrapped in a login screen. Agitation: That assumption creates platforms that cannot handle appointment surges, leak PHI through poorly designed Application Programming Interfaces (APIs), fail clinician workflow integration, and collapse the first time the hospital asks for an EHR connection. Solution: Design the platform as a layered distributed system from the first commit. This article gives you the full blueprint, including the five architecture layers, the real-time data pipeline, compliance controls, and the exact tech stack Acquaint Softtech deploys for telehealth clients across the US, UK, Australia, and the UAE. |
The confusion around how does telemedicine works technically exists because two very different products wear the same label. One is a video conferencing tool with a doctor on the other end. The other is a regulated clinical system that happens to include video. The first can be built in six weeks. The second takes six months minimum and requires custom telehealth platform development grounded in healthcare workflow engineering, not generic web development. This article defends the second definition because the first does not survive contact with a real hospital billing cycle, a clinician's documentation requirement, or a patient's continuity-of-care expectation.
The first section below defines the system boundaries before we get into the layers. If you skip it, the rest of the article will read like a tech stack list instead of an architecture blueprint. For teams that need the deeper strategic context, our master guide to healthcare software development in 2026 covers the wider landscape that this sub-pillar sits inside.
What a Telemedicine App Actually Is: System Boundaries and Real Definition

A telemedicine app is a clinical system that lets a licensed healthcare provider deliver diagnosis, advice, prescription, or ongoing care to a remote patient through synchronous video, asynchronous messaging, or store-and-forward data exchange, while preserving the full regulatory, documentation, and billing obligations of an in-person visit. The last clause is the one that separates telemedicine from video chat. A telemedicine app does not just connect people. It produces a medical encounter record.
The four system boundaries
Before you draw a single architecture diagram, name the four environments the system must move data between. Every telemedicine platform is a coordination layer across these four.
Direct AnswerA telemedicine app works by coordinating data between four environments: the patient environment (mobile or web client), the provider environment (clinician dashboard plus Electronic Health Record connection), the platform environment (backend services, video relay, and storage), and the payer environment (insurance and pharmacy networks). Data flows through encrypted channels with consent logged at each handoff. |
Patient environment
The consumer-facing app runs on iOS, Android, or a web browser. It captures identity, consent, vital inputs, symptoms, payment method, and video or chat sessions. Built in React Native, Flutter, or a Progressive Web App (PWA), depending on reach requirements. The Acquaint team has shipped all three patterns for telehealth clients, and we choose based on bandwidth and device profile, not fashion.
Provider environment
The clinician-facing dashboard is typically a React or Vue.js web application tuned for a two-monitor setup. It holds the consultation queue, the patient chart, the prescription module, the EHR synchronization panel, and the documentation templates. Provider environments are where your decision to hire Python developers or hire MERN stack developers decisions have the largest impact on velocity because clinicians use this screen for six hours a day.
Platform environment (the core)
The backend services cluster is running in a Health Insurance Portability and Accountability Act (HIPAA) eligible cloud region. It contains the scheduling service, the video relay controller, the consent service, the clinical notes service, the prescription service, the billing service, the audit log service, and the message broker that stitches them together. This is where 70 percent of the engineering effort lands.
Payer and partner environment
The external network the platform must integrate with: pharmacy chains for e-prescription, insurance clearinghouses for eligibility and claims, laboratory providers for orders and results, and the hospital's existing EHR for encounter write-back. These integrations use Health Level Seven Fast Healthcare Interoperability Resources (HL7 FHIR) APIs and legacy HL7 v2 feeds. Underestimating this boundary is the single most common architectural mistake.
Boundary check before buildIf your development partner's architecture diagram does not clearly separate these four environments with explicit data flow arrows and a consent checkpoint at each boundary, the design is not production-grade. Ask for a revision before a line of code is written. |
The Five Architecture Layers: A Blueprint You Can Commission From
Every telemedicine platform Acquaint Softtech has shipped, from a pediatric clinic's Minimum Viable Product (MVP) to a multi-hospital consolidated platform, uses the same five-layer reference architecture. The layers exist for separation of concerns, independent scaling, and compliance audit isolation. If a single service handles video, billing, and PHI storage, the platform cannot pass a security review.
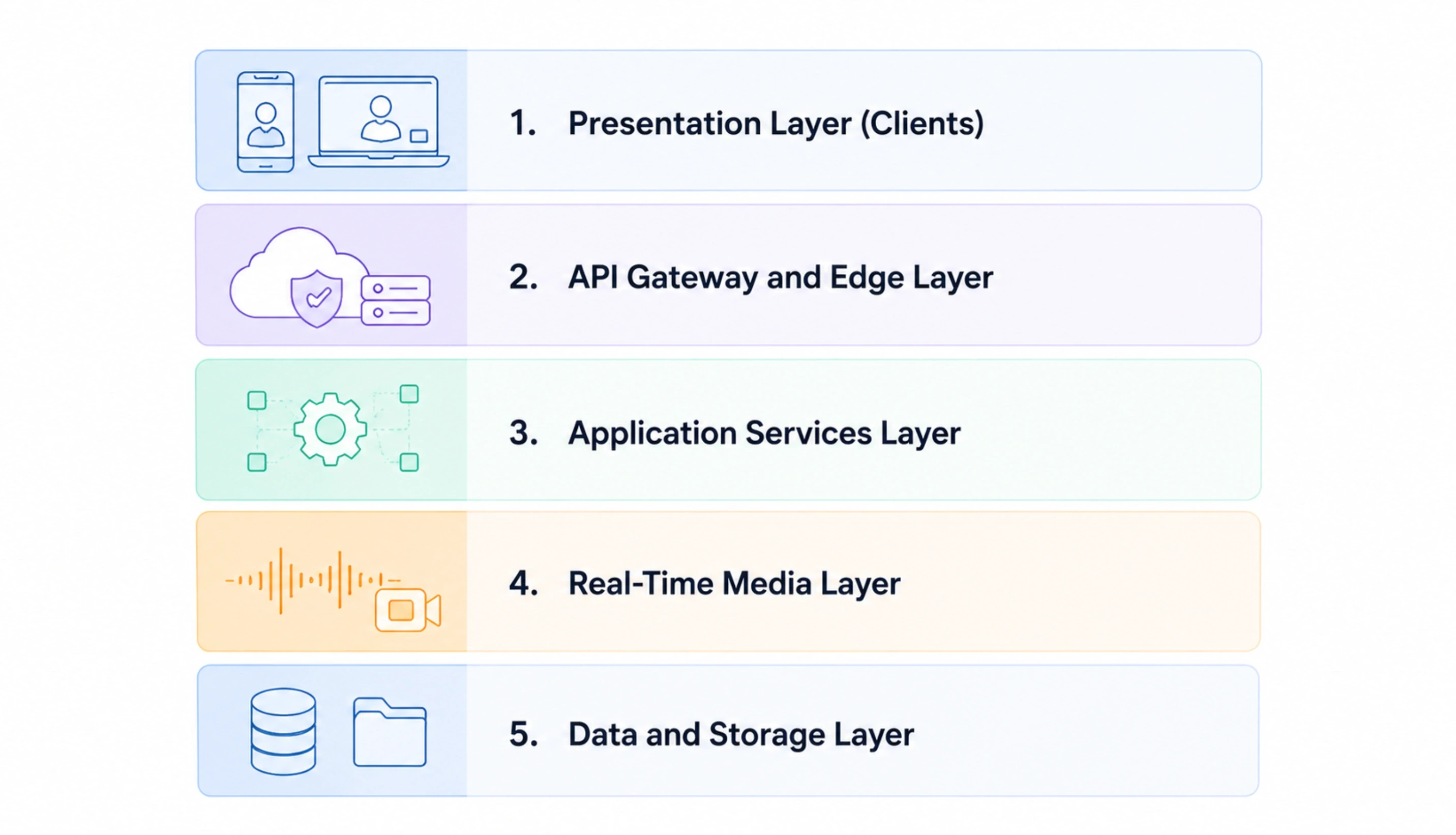
The Five Layers of a Production Telemedicine Platform
Presentation Layer (Clients):
The patient mobile app, the clinician web dashboard, and the administrator console. Stateless where possible. Written in React Native for patients (single codebase across iOS and Android), React or Vue.js for clinicians, and a lightweight admin in the same web framework. No PHI persisted in the client cache beyond the active session.
API Gateway and Edge Layer:
An API gateway (Amazon Web Services API Gateway, Kong, or Apigee) that handles authentication, rate limiting, request validation, and traffic routing to downstream services. OAuth 2.0 with Open Authorization Identifier Connect (OIDC) for session tokens. Web Application Firewall (WAF) in front to reject common injection patterns. Transport Layer Security (TLS) 1.3 only.
Application Services Layer:
The microservices that hold the clinical logic: scheduling, consultation, prescription, billing, messaging, notification, and consent. Each service owns its own database. Communication is synchronous, Representational State Transfer (REST) or Google Remote Procedure Call (gRPC) for request-response and asynchronous events through Apache Kafka or AWS Simple Notification Service (SNS) for state changes.
Real-Time Media Layer:
The video and audio relay path. Web Real-Time Communication (WebRTC) with a Selective Forwarding Unit (SFU) such as mediasoup, Janus, or Jitsi Videobridge. This layer is physically separated from PHI storage. The media never touches the clinical database. Signaling goes through the application services layer, but the media stream goes peer-to-server-to-peer.
Data and Storage Layer
The persistence tier. Operational PostgreSQL for transactional clinical data, separate schemas per service. Amazon Simple Storage Service (S3) with Server-Side Encryption for consultation recordings and document attachments. Redis for session cache and queue state. A dedicated audit log store (immutable, append-only) for compliance replay. Every bucket, schema, and index lives inside a HIPAA-eligible account with customer-managed encryption keys.
Layer responsibilities at a glance
The table below summarises the ownership model. Use it when commissioning a vendor. If they cannot name which service owns which function, they are designing as they build.
Layer | Primary Responsibility | Typical Tech | Failure Impact |
Presentation | User interface and input capture | React Native, React, Vue.js | Degraded user experience, not clinical |
API Gateway | Authentication, routing, and rate limiting | AWS API Gateway, Kong | Platform-wide outage |
Application Services | Clinical workflow logic and state | Node.js, Django, Laravel | Feature-level outage |
Real-Time Media | Video, audio, screen-share relay | WebRTC + mediasoup/Janus | Consultations drop, platform survives |
Data and Storage | PHI persistence, audit, cache | PostgreSQL, S3, Redis | Data loss, regulatory incident |
The closing principle is simple: a telemedicine platform should be able to lose the media layer entirely and still preserve the clinical record. If a dropped call erases a consultation note, the design is wrong. Understanding why EMR architecture must remain independent of your communication layer is the foundation before any media decision gets made. Teams evaluating this structure against a simpler approach should then read our comparison of WebRTC vs Twilio vs custom video for clinics before committing to a media vendor.
The Data Flow: Tracing a Single Consultation From Login to Payout
Architecture diagrams show where things live. Data flow diagrams show how they move. Below is the actual sequence for a single telemedicine consultation, from the moment a patient opens the app to the moment the clinician is reimbursed. Every step is a real API call or message bus event in a production system we ship.
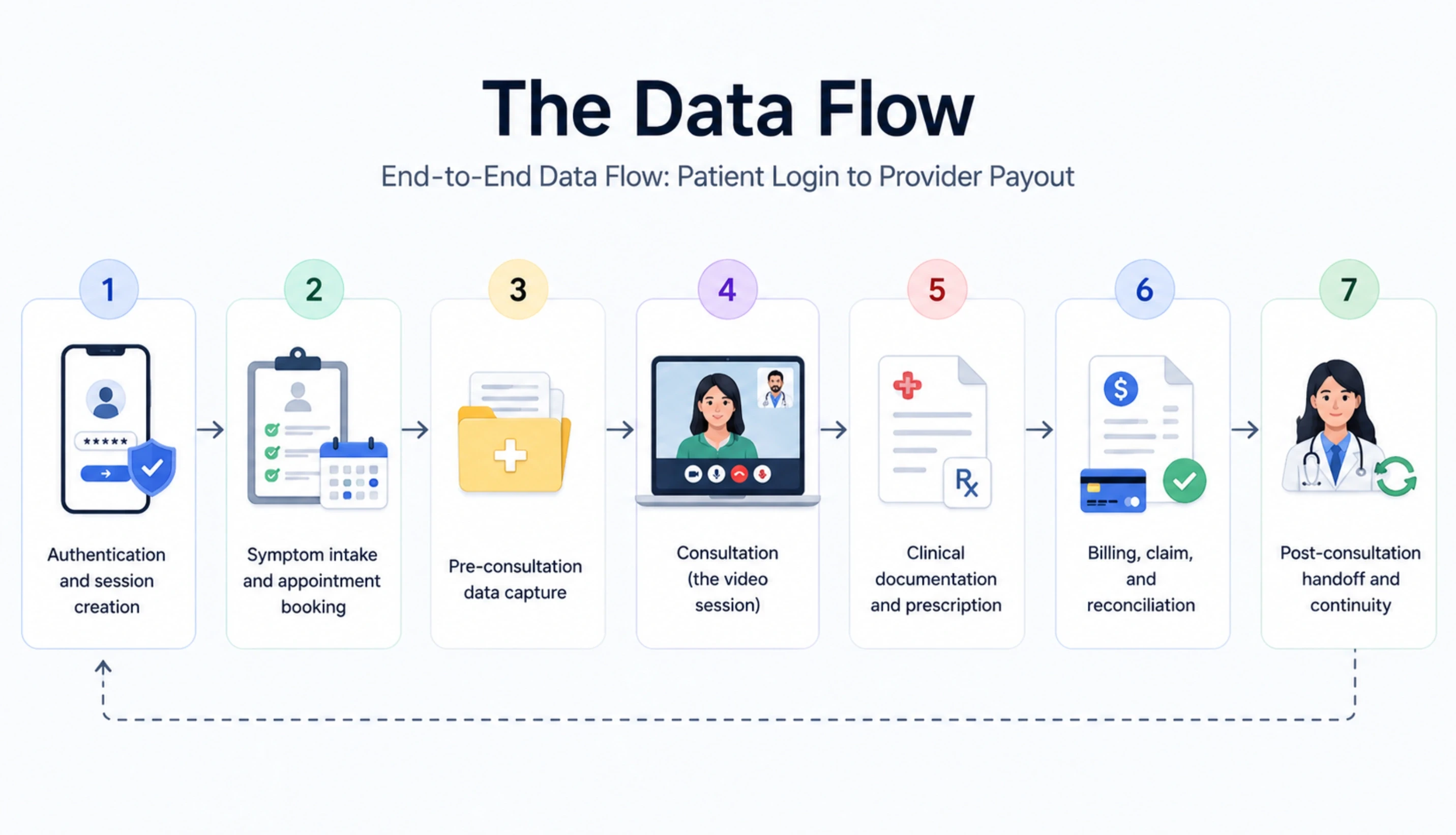
End-to-End Data Flow: Patient Login to Provider Payout
Authentication and session creation:
The patient opens the app. The client sends credentials (email plus one-time password, biometric, or Single Sign-On) to the API gateway. The identity service validates and returns a short-lived JavaScript Object Signed Notation (JSON) Web Token (JWT). Every downstream call now carries this token. Session audit event is written to the audit log service. Elapsed time: under 300 milliseconds.
Symptom intake and appointment booking:
The patient selects a symptom, specialty, or existing provider. The scheduling service queries available slots based on clinician roster, time zone, and license state (critical in the United States). A slot is reserved with a soft lock. Payment pre-authorisation runs through Stripe, Adyen, or a healthcare-specific processor. Consent form (telehealth-specific, jurisdiction-specific) is presented and signed digitally. Consent record is written to the consent service, cryptographically hashed.
Pre-consultation data capture:
15 minutes before the call, the patient receives a prompt to upload vitals (blood pressure, temperature, oxygen saturation) from a connected wearable or manual entry, plus any relevant photos or documents. These uploads go directly from client to S3 via pre-signed URLs. The clinical notes service receives a metadata event, never the file bytes. Photos are tagged as PHI and encrypted with a per-object key.
Consultation (the video session):
At the scheduled time, both parties join the video room. The signaling server matches them, WebRTC negotiates the peer connection, and the SFU starts relaying media. The clinician's dashboard opens the chart from the EHR via a FHIR Observation and Encounter read. Meanwhile, the audit log captures 'consultation started' with both participants' identifiers, timestamps, and device fingerprints. If recording is enabled (with explicit patient consent), it writes to S3 with separate Key Management Service (KMS) encryption.
Clinical documentation and prescription:
During or immediately after the call, the clinician writes Subjective, Objective, Assessment, Plan (SOAP) notes into the consultation service. Structured fields (diagnosis code using International Classification of Diseases 10 (ICD-10), procedure code using Current Procedural Terminology (CPT), medications) go into the EHR write-back queue. If a prescription is issued, the e-prescription service transmits it via Surescripts, National Council for Prescription Drug Programs (NCPDP) SCRIPT, or a regional equivalent to the patient's chosen pharmacy.
Billing, claim, and reconciliation:
The billing service composes the encounter into an X12 837 claim (United States) or the regional equivalent. It checks eligibility against the clearinghouse, submits the claim, and writes a billing event. The patient's co-pay is captured. The provider dashboard shows the claim status. When the payer adjudicates and remits via 835, the reconciliation service closes the loop. Total round trip: minutes to days, depending on payer speed.
Post-consultation handoff and continuity:
The patient receives an encounter summary, a link to the prescription status, and a follow-up scheduling prompt. The clinical note is finalised and written to the primary EHR. The audit log is closed for the encounter. A new care plan task may be created if the clinician marked one. Every event in steps 1 to 7 is now replayable from the audit log for a compliance review.
The 200-millisecond ruleIn a well-engineered telemedicine platform, each synchronous API hop should complete in under 200 milliseconds at the 95th percentile. Anything slower breaks the clinician's documentation flow and creates the single biggest complaint in provider surveys: 'the app feels slow'. Measure this from the start. |
This data flow is how every consultation on every telemedicine platform must behave. If your current vendor cannot draw this flow for you with the services named, they are not engineering a clinical system; they are assembling features. Teams that are still in the planning stage and weighing what building a custom healthcare platform actually costs may find that context useful before scoping the e-prescription leg. For a deeper look at how we implement that leg specifically, see our guide to adding e-prescribing to a telemedicine platform.
Stuck on the Data Flow Design?
Our architects will walk through the exact data flow for your specialty (general practice, mental health, chronic care, pediatric, specialty care) in a 45-minute working session, free, no pitch. We will hand over a marked-up sequence diagram at the end. Typical turnaround from request to call: 48 hours.
The 2026 Tech Stack: Opinionated Choices and Why
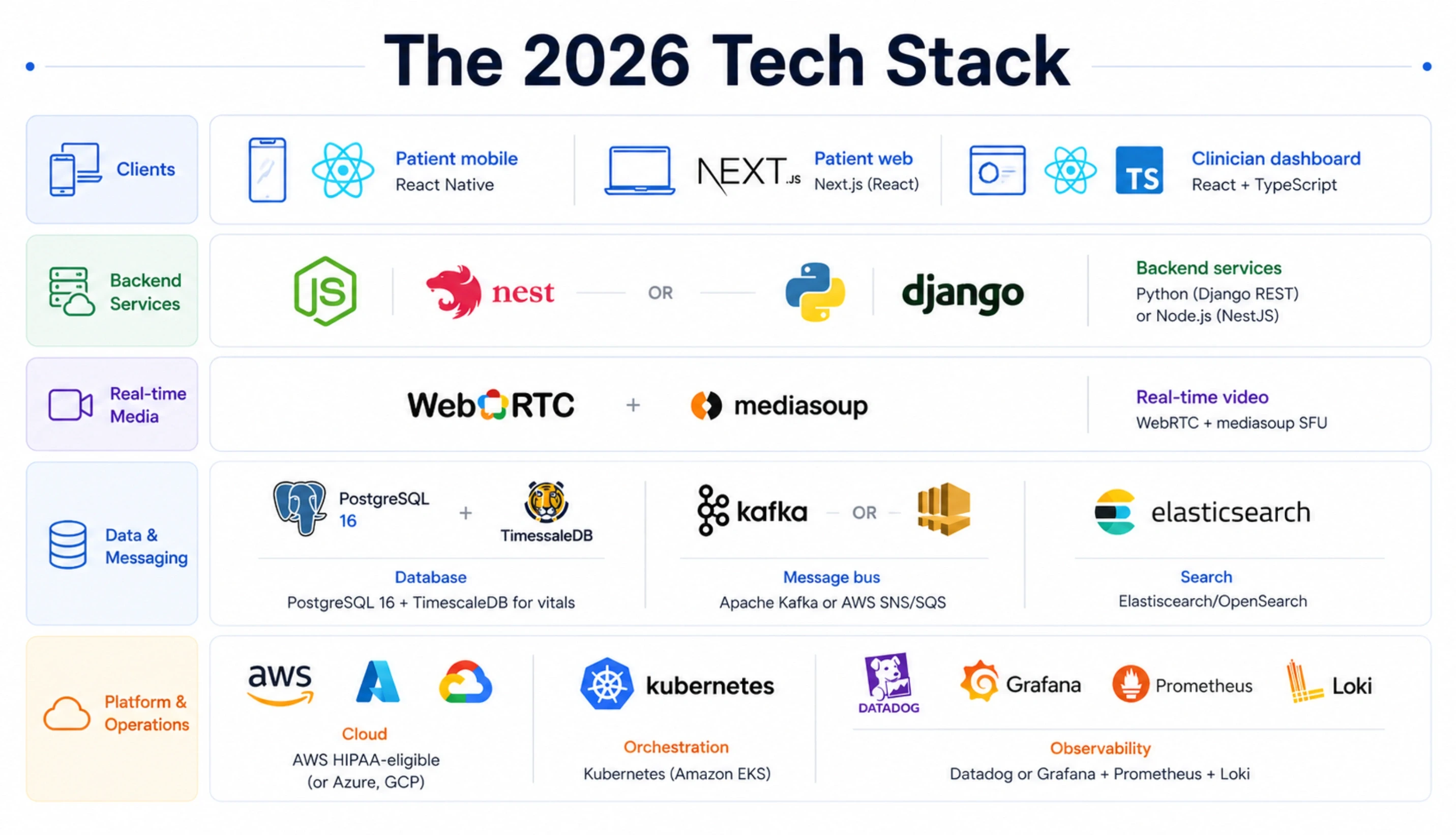
The telehealth platform tech stack 2026 question does not have a single answer. It has an opinionated default that works for 80 percent of use cases, and a set of decision points for the other 20 percent.
Below is the default stack Acquaint Softtech deploys for a mid-sized telemedicine platform targeting 5,000 to 50,000 monthly consultations.
Layer | Default Choice | Swap If... |
Patient mobile | React Native | Deep camera or Bluetooth Low Energy (BLE) wearable integration is core, then native iOS and Android |
Patient web | Next.js (React) | Clinic uses the existing Laravel ecosystem, then Laravel Livewire plus Inertia |
Clinician dashboard | React + TypeScript | Team has a strong Vue.js background, then Vue 3 with Pinia |
Backend services | Python (Django REST) or Node.js (NestJS) | Heavy Artificial Intelligence (AI) workload or scientific computing, then Python wins |
Real-time video | WebRTC + mediasoup SFU | Under 500 daily consultations, then Twilio Programmable Video reduces operational load |
Database | PostgreSQL 16 + TimescaleDB for vitals | Massive document load, then MongoDB for notes only |
Message bus | Apache Kafka or AWS SNS/SQS | Startup scale, then Redis Streams is sufficient |
Search | Elasticsearch/OpenSearch | Limited clinical search needs, then PostgreSQL full-text |
Cloud | AWS HIPAA-eligible (or Azure, GCP) | European Union (EU) data residency required, then regional sovereign cloud |
Orchestration | Kubernetes (Amazon EKS) | Small team, then Amazon Elastic Container Service with Fargate |
Observability | Datadog or Grafana + Prometheus + Loki | Cost sensitivity, then open-source stack |
A note on Python vs Node.js for the backend: we have shipped both. Python, especially with Django REST Framework plus Celery, wins when the platform will eventually add AI symptom triage, medical image inference, or clinical Natural Language Processing (NLP). Teams planning that layer should explore our AI development services for healthcare-specific model integration patterns.
Node.js with NestJS wins when the team is already full-stack JavaScript and the workload is primarily Create, Read, Update, Delete (CRUD) plus real-time messaging. If you are deciding between stacks for a fresh build, our comparison of PHP vs Python vs Node.js for SaaS 2026 walks through the long-tail tradeoffs.
On the infrastructure side, the choice between AWS, Azure, and Google Cloud Platform (GCP) matters less than you think for a telehealth platform. All three are HIPAA-eligible. AWS has the broadest HealthLake and Comprehend Medical service set. Azure has stronger enterprise hospital integrations. GCP Healthcare API has the cleanest FHIR implementation.
Pick based on your target customers' existing cloud, not on marketing. When clients need senior infrastructure expertise inside the team, we hire dedicated DevOps engineers who have built HIPAA-compliant Kubernetes clusters before, not generalists.
Authoritative referenceFor the official HIPAA cloud computing guidance, see the Health and Human Services cloud guidance. For FHIR implementation, the HL7 specification at hl7.org/fhir is the canonical source. Design decisions should reference these, not blog posts. |
Compliance Inside the Architecture: HIPAA, Consent, and Audit Trails
Compliance is not a module. It is a property that emerges from how the architecture is drawn. Telemedicine platforms that treat HIPAA as a 'checklist at the end' always fail their first audit. The ones that treat it as a set of architectural invariants pass on the first try. Here are the invariants Acquaint Softtech's architects apply to every telehealth build.
The five compliance invariants
Encryption in transit and at rest, always
TLS 1.3 everywhere, including service-to-service traffic inside the Virtual Private Cloud (VPC). Databases encrypted with customer-managed KMS keys. S3 buckets with Server-Side Encryption using Customer Master Keys (SSE-KMS). Backups encrypted separately with a different key. No exception, no 'internal network is fine' shortcut. The United States Department of Health and Human Services guidance at hhs.gov makes this non-negotiable.
Least-privilege access with break-glass
Every service account and human user holds the minimum permissions required. Access to raw PHI tables is logged. Emergency 'break-glass' access exists but generates an immediate alert to the compliance officer and a mandatory post-incident review. Privileged access is rotated quarterly.
Immutable audit logs for every PHI touch
Every read, write, and access attempt on a PHI record is logged to an append-only store. Logs include user identifier, timestamp, action, record identifier, and source Internet Protocol (IP). Logs are retained for a minimum of six years (HIPAA requirement) and are themselves encrypted. A failed audit is a failed platform.
Consent as a first-class service
Consent is not a checkbox on signup. It is a versioned, timestamped, cryptographically signed record that lives in a dedicated service. When the platform's terms change, the consent service tracks exactly which version each patient agreed to and when. This is the single most overlooked piece of compliance architecture and the first thing auditors ask for.
Data residency and Business Associate Agreement (BAA) boundaries
Every third party that touches PHI (video provider, analytics vendor, customer support tool, email provider) must have a signed BAA in place. Data must stay in the customer's required region. No 'quick sentiment analysis with a public AI API' shortcut. If it touches PHI, it has a contract and a boundary.
Compliance-aware development, not compliance-retrofitAt Acquaint Softtech, every senior developer assigned to a telehealth project goes through internal HIPAA-aware development training. We have seen too many platforms where compliance was bolted on in month 11 and the client then spent another four months re-architecting. Do it on day one. |
The compliance posture above is the minimum for a United States platform. For the United Kingdom, add UK General Data Protection Regulation (GDPR) and National Health Service (NHS) Data Security and Protection Toolkit compliance. For the European Union, add GDPR Article 9 special-category processing. For the UAE, add the UAE Federal Health Data Law. Acquaint Softtech has shipped across all four regulatory regions, and the architecture stays consistent; only the specific controls shift.
What Does a Custom Telemedicine Platform Cost to Build in 2026?
The custom telehealth platform development cost question has a wide range because telehealth platforms cover everything from a single-specialty MVP to a multi-tenant hospital system. Below are the real 2026 ranges Acquaint Softtech quotes, based on the last 18 months of telehealth engagements across the US, UK, Australia, and the UAE.
Build Type | Scope | Timeline | Investment Range (USD) |
Telehealth MVP | Single specialty, patient app + clinician web, basic billing, 2 integrations | 3-4 months | $45,000 - $85,000 |
Production v1 | Multi-specialty, EHR integration, e-prescription, and insurance billing | 6-9 months | $120,000 - $240,000 |
Enterprise platform | Multi-tenant, multi-region, full EHR write-back, advanced analytics, AI triage | 10-16 months | $280,000 - $650,000 |
Each range includes design, engineering, DevOps, QA, project management, security review, and a 90-day post-launch support window. It excludes third-party licenses (video SDK if used, clearinghouse subscription, EHR vendor fees) and ongoing hosting. Based on Acquaint Softtech's delivery operations across 1,300 plus projects, clients typically save 40 percent versus equivalent in-house builds in the US or UK at senior-level quality.
What the Acquaint telemedicine engagement includes
Five-layer architecture design document with explicit data flow diagrams reviewed by a senior architect and a clinical domain expert.
HIPAA-aware development practices, including mandatory encryption, audit logging, and consent service from sprint one, not bolted on later.
A dedicated product team structure with a tech lead who owns composition, performance, and continuity. Replacement is a vendor obligation, not a client renegotiation.
Sprint cadence with weekly demo, fortnightly retrospective, and a live Jira board the client owns read access to from day one.
Pre-integrated testing harness for HL7 FHIR endpoints, WebRTC load profiles, and synthetic PHI datasets.
Deployment to the client's HIPAA-eligible cloud account with Infrastructure as Code (IaC) in Terraform, handed over at the end of the engagement.
A 90-day post-launch defect resolution window with named engineers and a 24-hour severity-1 response.
The rate the client pays is the rate. No additional employer overhead on top. If the engagement ends, the Terraform, the code, the architecture diagrams, the runbooks, and the audit log schema all belong to the client. That is a contract term in every Acquaint engagement, not a negotiation point. Founders looking to go from a napkin idea to a working MVP should look at our MVP development services company for telehealth-specific packages.
Ready to See What Your Telemedicine Build Would Cost?
Share a one-page brief (target specialty, user scale, must-have integrations, target launch date), and we will return a tiered proposal with a transparent team structure, week-by-week plan, and fixed weekly rate within 48 hours. You interview every developer before they join the team.
The 7 Architecture Pitfalls That Kill Telemedicine Startups

From reviewing dozens of failed or struggling telehealth builds before Acquaint Softtech was brought in to rebuild them, the same seven mistakes appear over and over. Each one is architectural, which means reversing it requires a rewrite, not a patch.
Avoid These 7 Telemedicine Architecture Mistakes
Coupling video to the clinical database
The video SFU and the PHI database share the same VPC subnet, the same credentials, or worse, the same service. A media layer outage becomes a clinical outage. Fix: physical separation, different accounts where possible.
Building consent as a checkbox
Consent is stored as a boolean on the user table. There is no audit of which version was accepted. The first audit request ends the platform. Fix: a dedicated consent service with versioned templates.
No message bus from day one
All services call each other synchronously. The first time the e-prescription service slows down, the entire consultation hangs. Fix: introduce Kafka or SNS/SQS at MVP, not at scale.
Shared database across services
Every microservice reads and writes the same PostgreSQL instance. Schema changes require cross-team coordination. Scaling is impossible. Fix: one database per service, events for cross-service state.
Treating EHR integration as 'last sprint.'
The team builds the full platform, then tries to integrate with the hospital's Epic or Cerner in month nine. The integration is more complex than the entire rest of the app combined. Fix: stub the EHR integration from sprint one and validate with a real HL7 FHIR sandbox.
Ignoring observability until something breaks
There is no request tracing, no service-level indicator (SLI), and no structured logs. The first production incident takes 11 hours to diagnose. Fix: Datadog or Grafana + Prometheus + Loki configured before first deploy.
Mixing patient and clinician identity in one table
The 'users' table holds both. Role-based access becomes fragile. Authorization bugs leak PHI. Fix: separate patient and provider identity systems with distinct authentication flows and separate tables.
From the rebuild trenchesOf the seven mistakes above, the single most expensive to reverse is a shared database across microservices. A correctly-designed platform takes 6 weeks longer to build on day one and saves 6 months of rework by year two. That is not an opinion. That is Acquaint Softtech's measured delivery data across multiple telehealth rebuilds. |
For founders who want to understand the non-architectural failure patterns, team structure, regulatory gaps, and clinical workflow misfit, getting the healthcare team structure right from the start is the foundation that makes the rest solvable. Our architecture mistakes that sink telemedicine platforms cluster blog extends the list above with real teardown examples.
Worried Your Current Build Has One of These Pitfalls?
Send us your current architecture diagram and repository structure. A senior architect will do a two-hour review and flag the top three risks. No cost for the review. If you choose to remediate with Acquaint, we fold the review credit into the engagement. Turnaround: 48 hours from diagram receipt.
Real Engagement: How Acquaint Softtech Rebuilt a Failed Telehealth MVP
To make the architecture real, here is a recent telehealth engagement. Names and a few details are abstracted for confidentiality; the numbers and technical decisions are exact.
The situation
A founding team with domain expertise in mental health had commissioned a telehealth MVP from a generalist agency. Nine months and $110,000 in, they had a patient app, a doctor dashboard, and a video integration. They also had: no consent service, a single shared PostgreSQL for every service, no audit log, and a WebRTC setup that dropped calls at 20 concurrent sessions. Their clinical advisor had refused to sign off for HIPAA readiness. Launch was blocked.
What Acquaint did
A six-person Acquaint team (two backend, one mobile, one front-end, one DevOps, one tech lead) was deployed within 48 hours of engagement. The first four weeks were an architecture reset, not a code sprint. The team produced a five-layer architecture document, split the monolithic database into per-service schemas, stood up an audit log service, wrote a consent service with versioned templates, and introduced a mediasoup SFU behind Kafka signaling. In parallel, the mobile and front-end developers refactored the existing React Native app to call the new APIs. In weeks 5 to 14, the team shipped the remaining flows: e-prescription, insurance eligibility, clinician documentation, and hospital EHR integration through an HL7 FHIR adapter.
The measurable result
Outcome metrics after rebuild (month 4 post-relaunch) • Concurrent consultations supported: 20 → 450 (22x improvement) • Ninety-fifth percentile API response: 900 ms → 160 ms • HIPAA readiness audit: passed on first attempt • Cost to rebuild: $140,000 over 14 weeks (vs $110,000 wasted on the failed first build) • Consultation drop rate: 18% → 0.6% • Time to add a new specialty (pediatric): projected 12 weeks, actual 4 weeks, because the architecture supported it |
The principle the engagement illustrates is the one this entire article defends: how a telemedicine app works is an engineering question that must be answered before the first line of code, not discovered in production. For a similar pattern in a different industry, our case study on aviation safety software development for ASQS shows the same architectural-first approach applied to a regulated aviation audit platform.
Ready to Build a Telemedicine Platform That Survives 2026?
Whether you are at the napkin stage, mid-build and worried about architecture, or post-launch and hitting scale walls, Acquaint Softtech deploys senior telehealth engineers within 48 hours. Every team member has shipped HIPAA-compliant healthcare software before. You interview before you commit. Average tenure on telehealth accounts: 24 plus months.
Frequently Asked Questions
-
What technology stack is best for a telemedicine app in 2026?
The default Acquaint Softtech stack for a 2026 telemedicine platform is React Native for the patient app, React with TypeScript for the clinician dashboard, Python Django Rest Framework or Node.js NestJS for backend services, PostgreSQL with TimescaleDB for data, mediasoup on WebRTC for video, and Apache Kafka for the event bus, all deployed on an AWS HIPAA-eligible account with Kubernetes orchestration.
-
How is data transmitted in a telemedicine app?
Data moves through encrypted channels only. Application Programming Interface (API) traffic uses Transport Layer Security (TLS) 1.3 over HTTPS with short-lived JSON Web Tokens for authentication. Video and audio streams use Web Real-Time Communication (WebRTC) routed through a Selective Forwarding Unit with Datagram TLS (DTLS) encrypted peer connections.
-
What is the architecture of a telehealth platform?
A production telehealth platform has five layers: a presentation layer (patient and clinician clients), an API gateway and edge layer, an application services layer with clinical microservices, a real-time media layer physically separated from the clinical services, and a data storage layer with per-service databases and an append-only audit log. Services communicate synchronously through REST or gRPC and asynchronously through a message bus.
-
How much does it cost to develop a telemedicine app in 2026?
In 2026, a production-grade single-specialty telemedicine MVP built by Acquaint Softtech ranges from $45,000 to $85,000 over 3 to 4 months. A multi-specialty production v1 with Electronic Health Record (EHR) integration and insurance billing ranges from $120,000 to $240,000 over 6 to 9 months.
An enterprise-class multi-tenant platform with full EHR write-back and AI triage runs $280,000 to $650,000 over 10 to 16 months. These ranges include design, engineering, DevOps, QA, security review, project management, and a 90-day post-launch support window. They exclude third-party licenses and ongoing hosting.
-
How long does it take to build a telemedicine platform?
An MVP takes 3 to 4 months with a 4 to 5-person team. A production v1 takes 6 to 9 months with a 6 to 8-person team. An enterprise platform takes 10 to 16 months with a 10 to 14-person team. These timelines assume the architecture decisions are made before sprint one (which is Acquaint Softtech's standard practice) and that third-party integrations (EHR, e-prescription clearinghouse, insurance payer) are scoped at the start. Underestimating integration complexity is the single most common cause of telehealth timeline slippage in the industry.
-
Is it safe to outsource hiring telemedicine developers in India?
Yes, when the vendor has healthcare-specific engineering experience, Business Associate Agreements in place, developer-level HIPAA awareness training, and a track record of deployed telehealth products.
Acquaint Softtech has delivered telemedicine projects to clients in the United States, the United Kingdom, Australia, and the United Arab Emirates for over 13 years. The safety question is not about geography; it is about process discipline, contract structure, and whether the vendor has built this kind of system before. Ask for architecture diagrams from prior engagements before you sign.
-
What happens to my code and data if the telemedicine engagement ends?
Every Acquaint Softtech engagement contract specifies that the source code, Terraform infrastructure definitions, architecture documentation, runbooks, and audit schemas are the client's property from the moment they are produced.
-
Can a telemedicine app integrate with existing hospital EHR systems like Epic, Cerner, or Meditech?
Yes, through HL7 FHIR APIs for modern integrations and HL7 v2 messaging for legacy systems. Epic and Cerner both expose FHIR R4 endpoints for clinical read and write. Meditech supports a mix of FHIR and custom APIs.
Table of Contents
Get Started with Acquaint Softtech
- 13+ Years Delivering Software Excellence
- 1300+ Projects Delivered With Precision
- Official Laravel & Laravel News Partner
- Official Statamic Partner
Related Reading
Custom Healthcare Software Development: An End-to-End Guide
Custom healthcare software is revolutionizing the medical industry by providing tailored solutions that enhance patient care, streamline processes, and improve security. Discover the benefits, challenges, and step-by-step guide to building effective custom healthcare software. Learn how expert developers can help you stay ahead in the evolving healthcare landscape.

Mukesh Ram
February 27, 2025Healthcare & IT Staff augmentation - A success partnership
Healthcare IT staff augmentation bridges skill gaps and reduces workloads by hiring remote developers. This strategy enhances IT capabilities, ensuring smooth implementation and management of advanced technologies in healthcare organizations.

Mukesh Ram
August 6, 2024Proof of Concept: Why is it important in software development?
Discover how a Proof of Concept (PoC) can validate your project's feasibility, enhance stakeholder trust, and streamline development processes effectively.

Acquaint Softtech
April 28, 2025India (Head Office)
203/204, Shapath-II, Near Silver Leaf Hotel, Opp. Rajpath Club, SG Highway, Ahmedabad-380054, Gujarat
USA
7838 Camino Cielo St, Highland, CA 92346
UK
The Powerhouse, 21 Woodthorpe Road, Ashford, England, TW15 2RP
New Zealand
42 Exler Place, Avondale, Auckland 0600, New Zealand
Canada
141 Skyview Bay NE , Calgary, Alberta, T3N 2K6



